I’ve spent my entire career in technology sales. In fact, I’d estimate that I’ve written or reviewed more than a hundred various security questionnaire responses, risk assessments, vendor assessments, security assessments and technical RFPs. No matter what you call them, if you’re in technology sales you’ve likely had to complete a security questionnaire response, and like me, dreaded the process.
For sales, it feels like the security questionnaire is a hurdle between you and a signed contract. In my past experiences, this roadblock can delay the sales process for days, weeks or more. Every day that the potential client waits for a response is a day that the deal isn’t done. It’s a day for your competitors to get a foot in the door. That’s a frustrating prospect when the end of quarter looms. The entire sales team is coordinating with a few subject matter experts (SMEs) to wrap up loose ends and win deals before the books close.
It’s not a fun process for the experts who must respond to the questionnaires either. These lengthy documents are complex, technical and mind-numbingly repetitive. It’s like coming back into work after the weekend and answering the same question over and over again.
Luckily, there’s a way to make security questionnaires more bearable. But first, let’s explore why they exist, who is answering them and how you can get faster answers.
What does a security questionnaire accomplish?
While I don’t relish writing the security questionnaire response, I understand why they are so crucial. Costly data breaches happen daily and security should be on everyone’s mind. Businesses must protect themselves from risk and that means thoroughly vetting their vendors. Not only is the security questionnaire a part of the procurement process, but it’s also a recurring, annual exercise to ensure vendors remain compliant with the latest security updates.
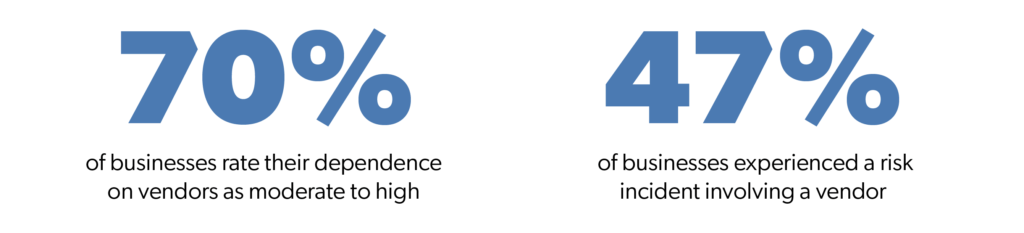
Vendor relationships are increasingly crucial to success. According to a recent survey by Deloitte, 70 percent of businesses rate their dependency on outside vendors as moderate to high. As a result of these increasingly close partnerships, vendors routinely interact with their clients’ sensitive data. Consequently, the same Deloitte survey indicated that 47 percent of businesses surveyed experienced a ‘risk incident’ involving an outside vendor.
This is why businesses take their security assessments so seriously and have made them a standard part of the procurement process.
The questionnaires are designed by the organization’s IT department and included cover a range of topics. Depending on the industry, surveys can range from around 30 to more than 300 questions.
Topics typically covered by the questionnaire include:
- Security audits and penetration testing
- Internal security practices and policies
- Personnel policies, hiring practices and training programs
- Security certifications
- SLAs and uptime vs. downtime
- Web application security
- Physical and datacenter security
- Infrastructure security
- Business continuity
As you might imagine, these surveys vary from company to company. But, all seek a clear answer to one question — can they trust you, the vendor, to protect their business’ data?
The long way to assessment responses
If the core purpose of these assessments is so straightforward, why is answering them so complicated? Because accuracy is vital. For example, if I submit an incorrect or out-of-date response, not only do I risk losing the sale, but it could also damage my company’s reputation or worse.
Even after years of answering assessments, I must admit that upon first viewing them, my eyes still glaze over. It’s just not my field of expertise, so I have to work with several departments and SMEs to get accurate and complete answers. A security questionnaire response may be routed through one, or all, of the product development, IT, customer support and legal departments.
Each of these experts takes time away from their primary responsibilities to do their part to answer the vendor questionnaires. After all the information has been collected, it must pass another review by a senior-level or executive approver before being submitted back to the potential client. Certainly, it can be a lengthy process.
Four tips for a faster security questionnaire response
A centralized place for answer content is the key to quick responses. Enlist your SMEs and create a knowledge base for common questions that pop up in every vendor assessment. You can start yours now with these basic questions. Or, take it to the next level with RFP software and quickly gather approved responses by uploading past completed questionnaires. Don’t forget! It’s crucial to have your experts and approvers conduct regular reviews to ensure that answers are kept up-to-date.
In a recent article by David Levine, Vice President of Information Security & CISO for Ricoh echoes this advice when discussing security questionnaires saying,
“Catalog the answers you are providing to help ensure consistent information is provided, review that information on a regular basis and add new answers as you see new questions.”
Like most salespeople, I want to remove roadblocks and deliver a great customer experience. Certainly, promptly returning your security questionnaire response is one way to build customer confidence not to mention shorten the sales cycle. Highly motivated and equipped with an RFP software to automate responses and a continually updated knowledge base, my sales team can confidently answer technical questions and escalate only new questions to SMEs.
When you do encounter new questions, make it simple and easy for your SMEs and approvers to collaborate so they aren’t tempted to set it aside for a day when they have more time to think about it. RPF technology offers real-time task management for answer editing, team collaboration and approvals.
Security questionnaires aren’t just issued by potential customers. Similarly, existing customers send annual assessments to ensure that they are proactively managing third-party risk. The knowledge base can be leveraged by the customer success team to quickly provide the most up-to-date information. Consequently, the renewal process is much shorter.
A new way to look at responding to security questionnaires
Using the knowledge base in our RFP technology has changed the way I view the security questionnaire response process. I don’t dread them but instead, think of them as a reason for optimism. Not only is the process entirely manageable, but it’s often a positive buying signal. In addition, my sales team is empowered with the intelligence and data to quickly and confidently answer questions that fall outside of their expertise using the knowledge base. So now, I don’t treat assessments as a distraction, but instead use them as a tool to differentiate.



